Which two technologies can secure the control plane of the Cisco router?
Which two technologies can secure the control plane of the Cisco router? (Choose two. r
Which of these statements is correct regarding user setup on ACS 4.0?
Cisco Secure Access Control Server (ACS) is a highly scalable, high-performance access control
server that provides a comprehensive identity networking solution. Which of these statements is
correct regarding user setup on ACS 4.0?
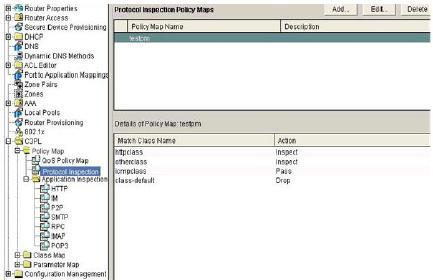
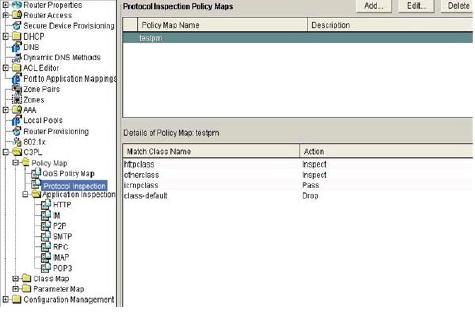
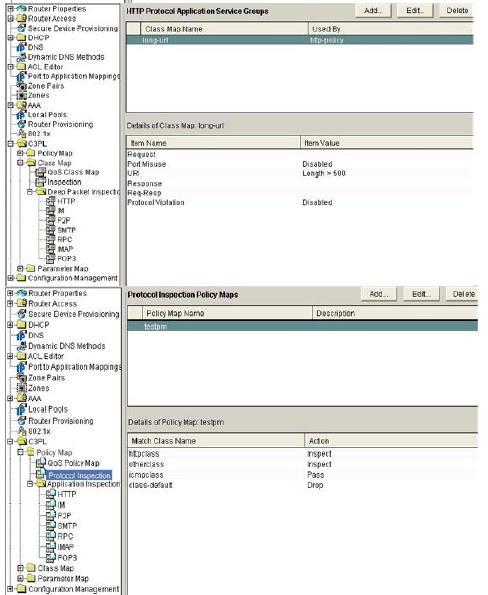
which two statements correctly describe the Cisco IOS Zone-Based Firewall configuration?
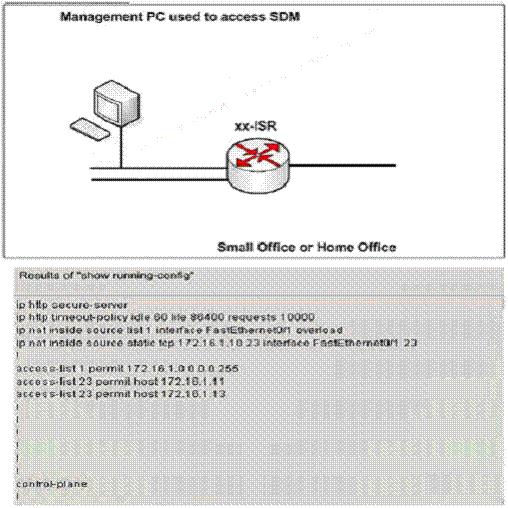
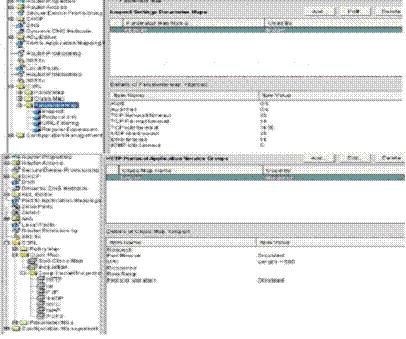
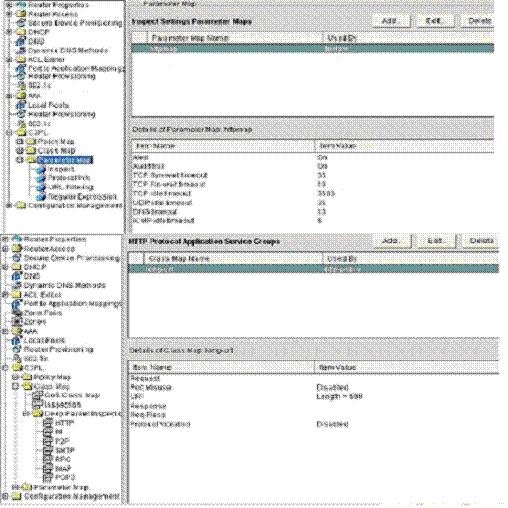
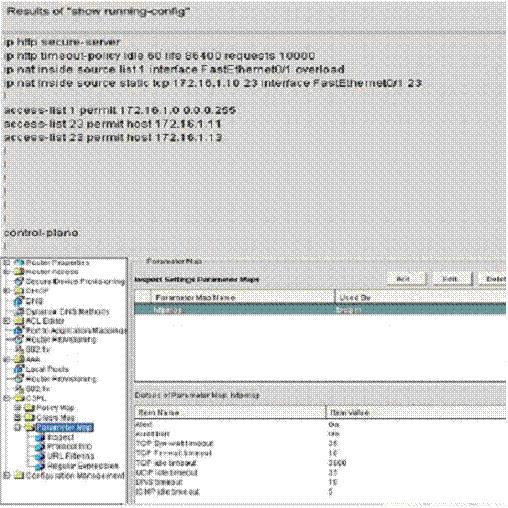
what is the User Datagram Protocol (UDP) idle time set for any HTTP traffic that is sourced from the "in&
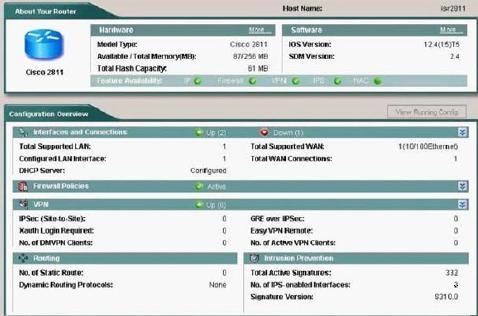
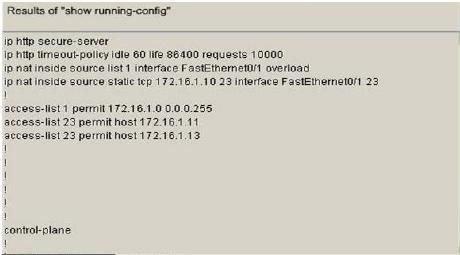
what is the reason that outside hosts can’t initiate Telnet (port 23) traffic to the 172.16.1.10 inside
Which two categoiy types are associated with 5.x signature use in Cisco IOS IPS?
Which two categoiy types are associated with 5.x signature use in Cisco IOS IPS? (Choose two.)
(Choose two)
Select two issues that you should consider when implementing IOS Firewall IDS. (Choose two)
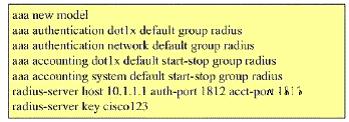
Which command is used to support 802.lx guest VLAN functionality based on the following configuration?
Why is the Cisco IOS Firewall authentication proxy not working based on the following configuration?
You are in charge of Securing Networks Cisco Routers and Switches in your company. Why is the
Cisco IOS Firewall authentication proxy not working based on the following configuration?
aaa new model
aaa authentication login default group tacacs
aaa authentication auth-proxy default group tacacs +
aaa accounting auth-proxy default start-stop group tacacs+
enable password TeSt_123
ip auto-proxy name pxy http
ip auto-proxy auth-proxy-banner
interface EthernetO/1
ip address 192.168.1.1 255.255.255.0
ip auto-proxy pxy
no ip http server
tacacs-server host 192.168.123.14
tacacs-server key Cisco
lOutput omitted
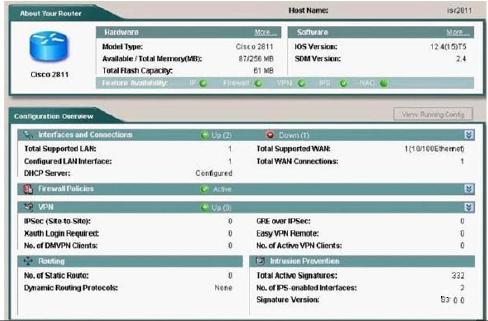
Which advantage can be obtained by implementing the Cisco IOS Firewall feature?
Which advantage can be obtained by implementing the Cisco IOS Firewall feature?