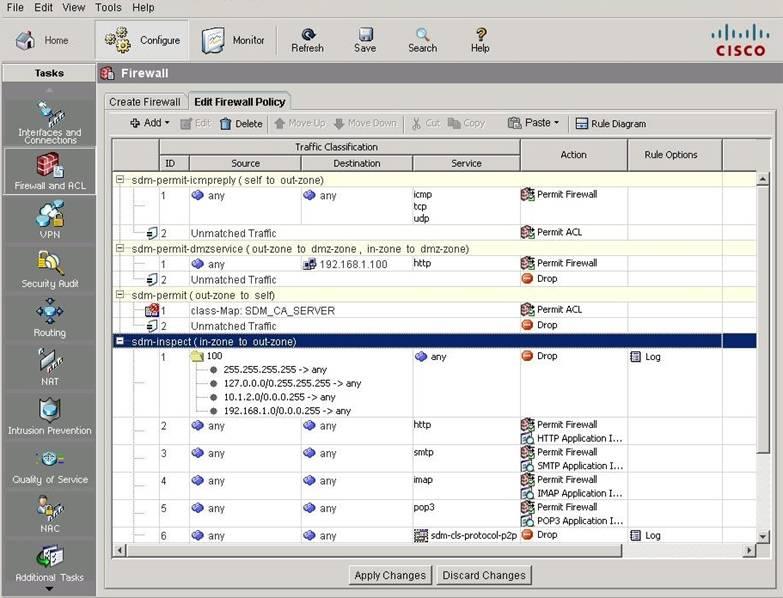
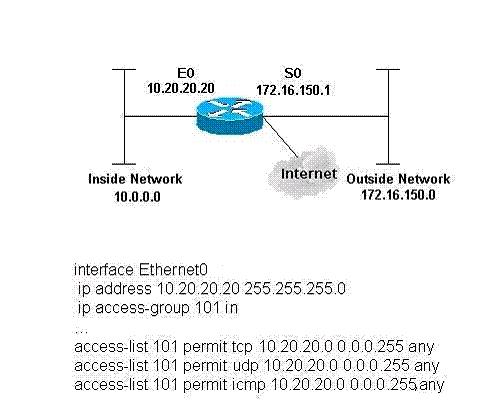
Which access list will permit HTTP traffic sourced from host 10.1.129.100 port 3030 destined to host 192.168.1
Which access list will permit HTTP traffic sourced from host 10.1.129.100 port 3030 destined to
host 192.168.1.10?
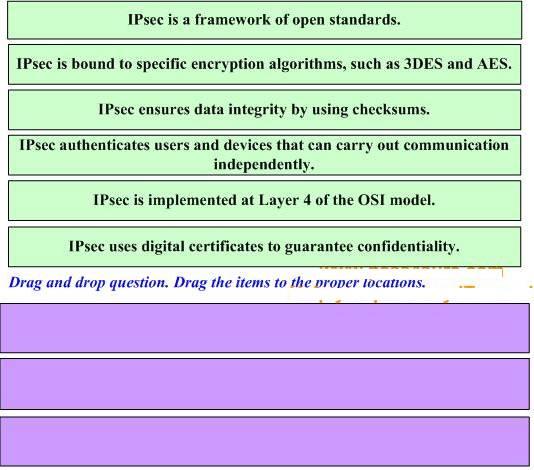
Drag three proper statements about the IPsec protocol on the above to the list on the below.
what percentage of the keyspace must an attacker generally search through until he or she finds the key that d
In a brute-force attack, what percentage of the keyspace must an attacker generally search
through until he or she finds the key that decrypts the data?
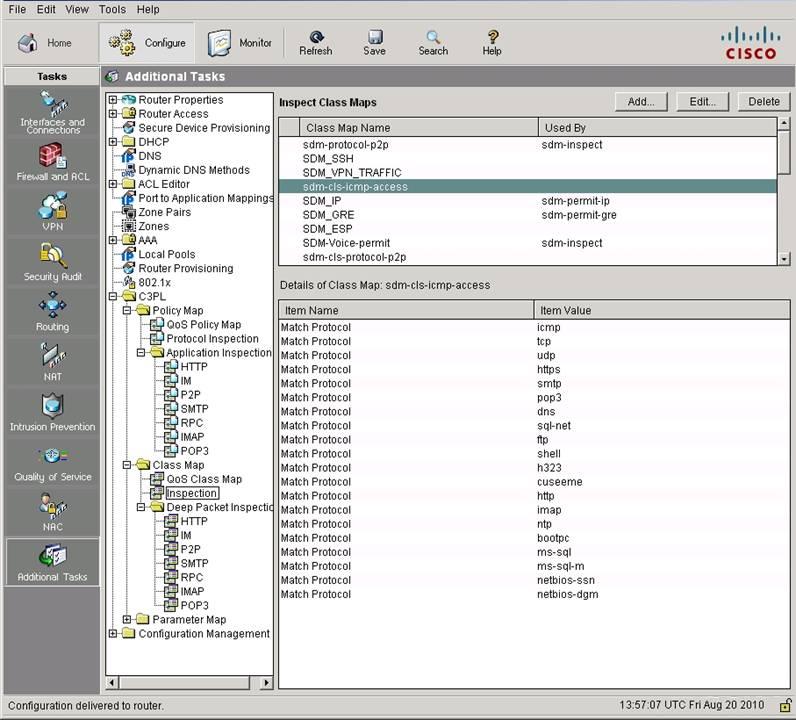
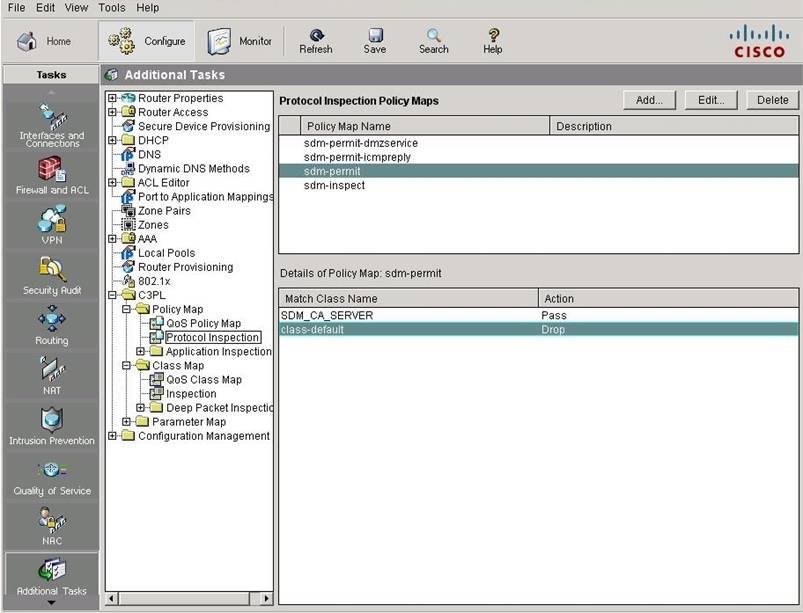
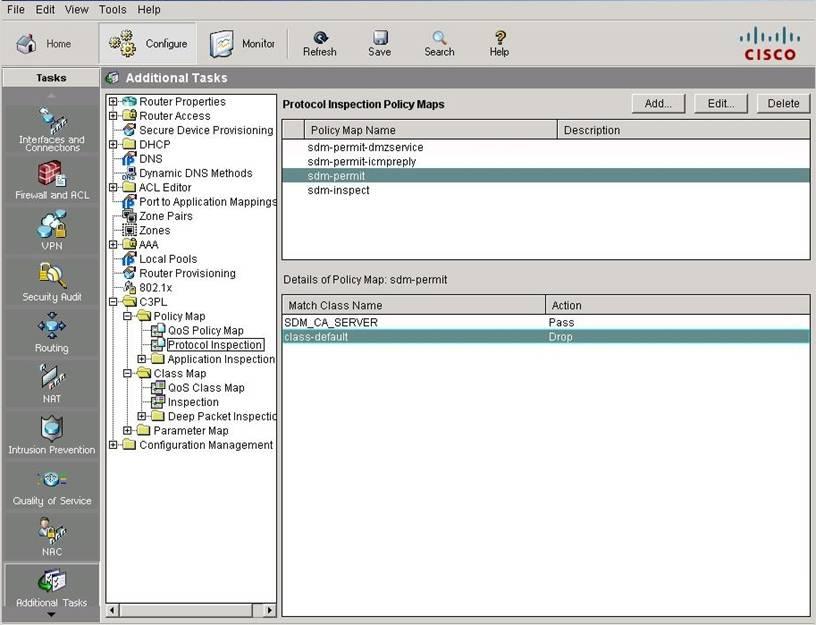
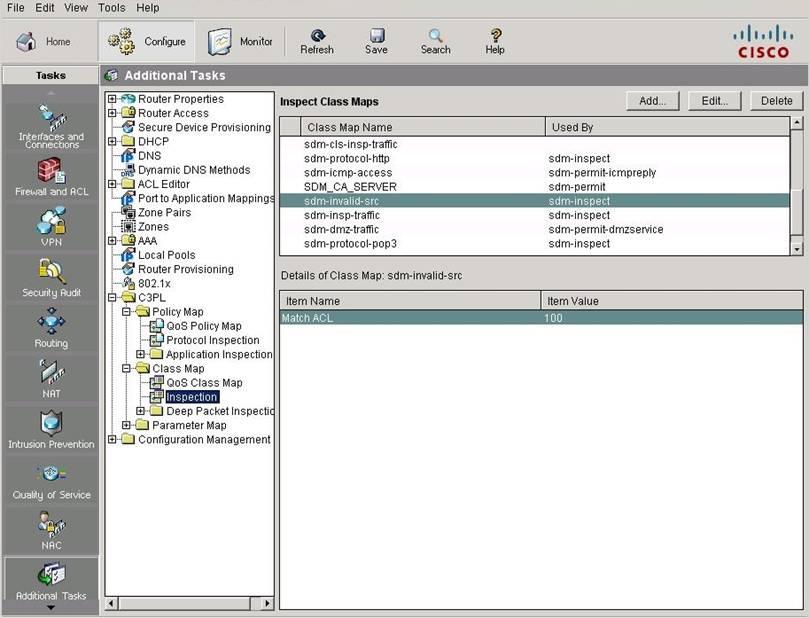
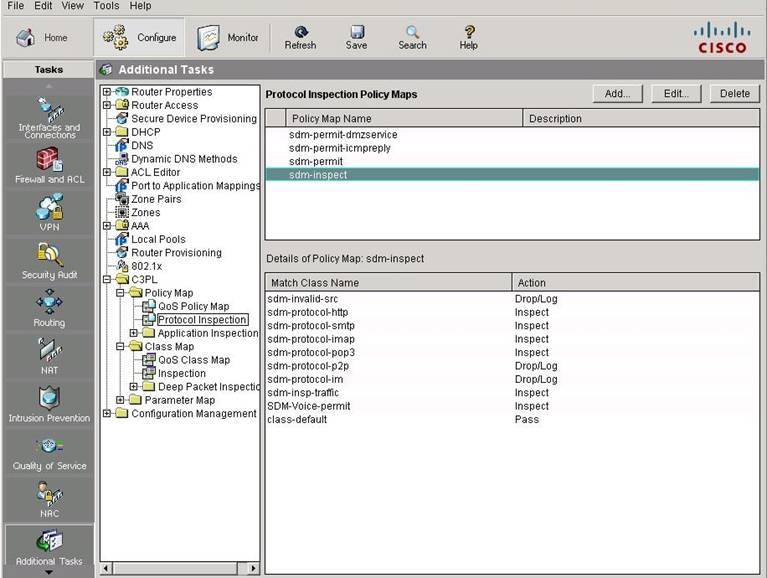
what is the action assigned to the traffic class "class-default"?
Which statement is true?
place the correct descriptions in the proper locations.
Which of these can be used to authenticate the IPsec peers during IKE Phase 1?
Which of these can be used to authenticate the IPsec peers during IKE Phase 1?
Which description about asymmetric encryption algorithms is correct?
Which description about asymmetric encryption algorithms is correct?
which management topology keeps management traffic isolated from production traffic?
For the following items, which management topology keeps management traffic isolated from
production traffic?
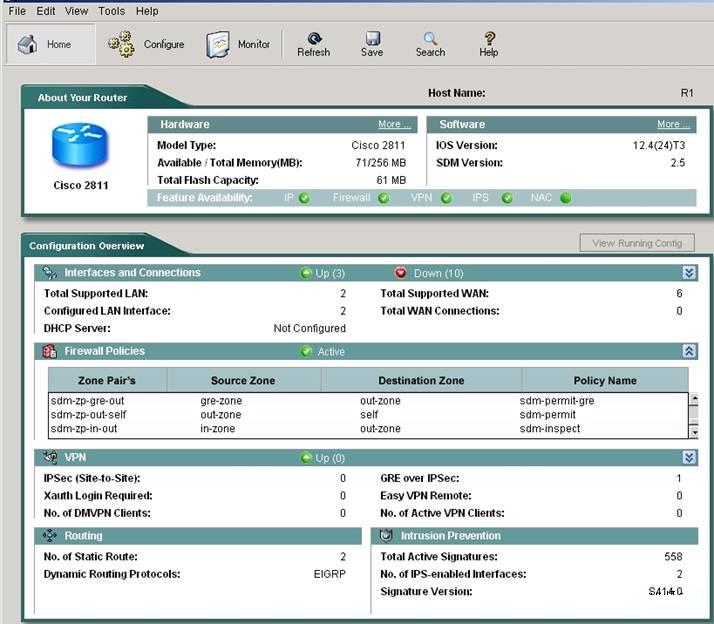
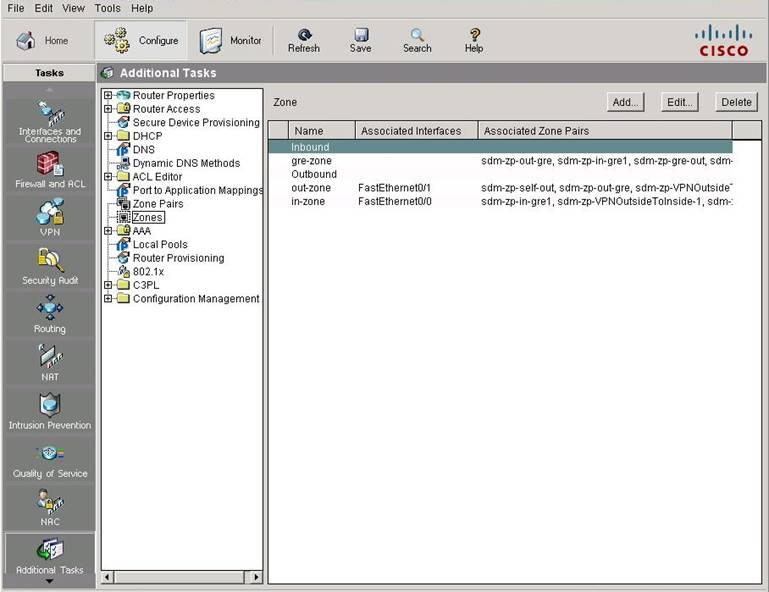
which type of tunnel?
You work as a network engineer, do you know an IPsec tunnel is negotiated within the protection
of which type of tunnel?