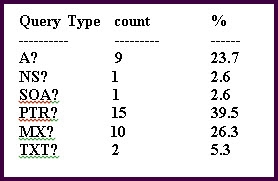
Which DNS Query Types pertains to email?
Which piece of information is critical to begin your network investigation?
A server administrator tells you that the server network is potentially under attack. Which piece of
information is critical to begin your network investigation?
Which describes the best method for preserving the chain of evidence?
Which describes the best method for preserving the chain of evidence?
Which will be provided as output when issuing the show processes cpu command on a Cisco IOS router?
Which will be provided as output when issuing the show processes cpu command on a Cisco IOS
router?
Which protocol is used in this network traffic flow?
Which two types of data are relevant to investigating network security issues?
Which two types of data are relevant to investigating network security issues? (Choose two.)
which event would qualify as having the highest severity?
In the context of a network security device like an IPS, which event would qualify as having the
highest severity?
Which event is likely to be a false positive?
Which event is likely to be a false positive?
which chain of alarms would be most concerning?
Given a Linux machine running only an SSH server, which chain of alarms would be most concerning?
which three alerts would be of concern?
If a company has a strict policy to limit potential confidential information leakage, which three alerts
would be of concern? (Choose three.)