Which four steps should Joe implement to accomplish this goal?
Joe was asked to secure access to the Cisco Web Security Appliance to prevent unauthorized access.
Which four steps should Joe implement to accomplish this goal? (Choose four.)
Which command is used to enable strong ciphers on the Cisco Web Security Appliance?
Which command is used to enable strong ciphers on the Cisco Web Security Appliance?
Which Cisco ESA command is used to edit the ciphers that are used for GUI access?
Which Cisco ESA command is used to edit the ciphers that are used for GUI access?
which two steps must be performed?
In order to set up HTTPS decryption on the Cisco Web Security Appliance, which two steps must be
performed? (Choose two.)
which four settings are inherited?
When a Cisco Email Security Appliance joins a cluster, which four settings are inherited? (Choose four.)
Which feature of the Cisco Email Security Appliance provides this record?
The helpdesk was asked to provide a record of delivery for an important email message that a customer
claims it did not receive. Which feature of the Cisco Email Security Appliance provides this record?
Which two features must be enabled in order to record those connections in the mail log on the Cisco ESA?
Connections are being denied because of SenderBase Reputation Scores. Which two features must be
enabled in order to record those connections in the mail log on the Cisco ESA? (Choose two.)
Which five system management and reporting protocols are supported by the Cisco Intrusion Prevention System?
Which five system management and reporting protocols are supported by the Cisco Intrusion Prevention
System? (Choose five.)
What is the likely cause of the intermittent delays?
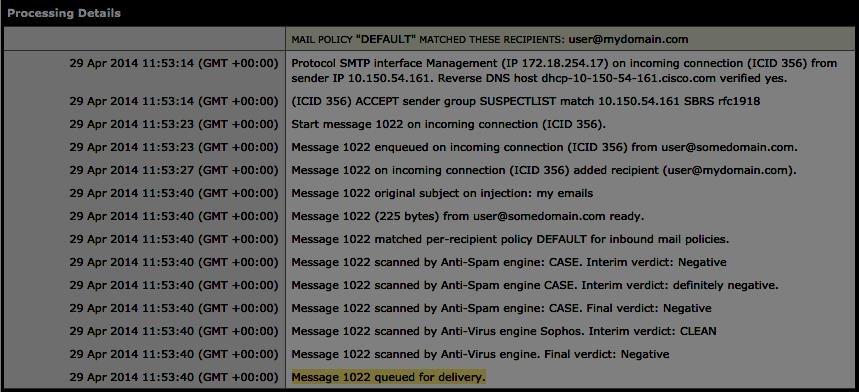
Refer to the exhibit.
The system administrator of mydomain.com received complaints that some messages that were sent
from sender user@somedomain.com were delayed. Message tracking data on the sender shows that an
email sample that was received was clean and properly delivered. What is the likely cause of the
intermittent delays?
Which tool on the Cisco Email Security gateway can you use to debug or emulate the flow that a message takes t
A system administrator wants to know if the email traffic from a remote partner will activate special
treatment message filters that are created just for them. Which tool on the Cisco Email Security gateway
can you use to debug or emulate the flow that a message takes through the work queue?