Which tool on the Cisco Email Security gateway can you use to debug or emulate the flow that a message takes t
A system administrator wants to know if the email traffic from a remote partner will activate special
treatment message filters that are created just for them. Which tool on the Cisco Email Security
gateway can you use to debug or emulate the flow that a message takes through the work queue?
Which command verifies that CWS redirection is working on a Cisco IOS router?
Which command verifies that CWS redirection is working on a Cisco IOS router?
Which two commands are used to verify that CWS redirection is working on a Cisco ASA appliance?
Which two commands are used to verify that CWS redirection is working on a Cisco ASA
appliance? (Choose two.)
Which two modes does Cisco recommend using to configure for this?
A user is deploying a Cisco IPS appliance in a data center to mitigate most attacks, including
atomic attacks. Which two modes does Cisco recommend using to configure for this? (Choose
two.)
Which statement about Cisco IPS Manager Express is true?
Which statement about Cisco IPS Manager Express is true?
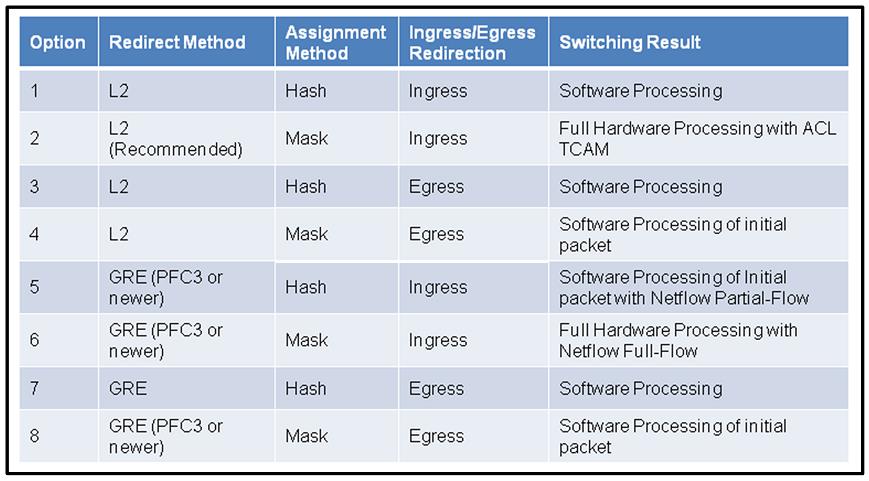
Which four rows identify the switch behavior in correlation to the redirect method?
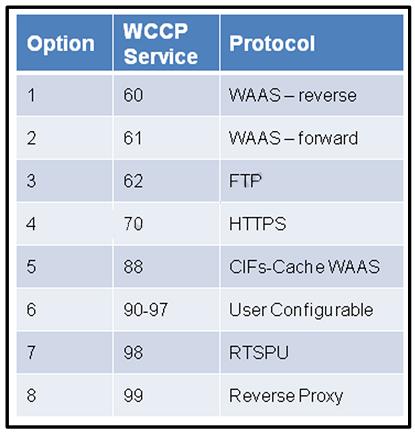
Which four rows exhibit the correct WCCP service to protocol assignments?
Which three protocols are required when considering firewall rules for email services using a Cisco Email Secu
Which three protocols are required when considering firewall rules for email services using a Cisco
Email Security Appliance? (Choose three.)
Which two design considerations are required to add the Cisco Email Security Appliance to an existing mail del
Which two design considerations are required to add the Cisco Email Security Appliance to an
existing mail delivery chain? (Choose two.)
Which three sender reputation ranges identify the default behavior of the Cisco Email Security Appliance?
Which three sender reputation ranges identify the default behavior of the Cisco Email Security
Appliance? (Choose three.)