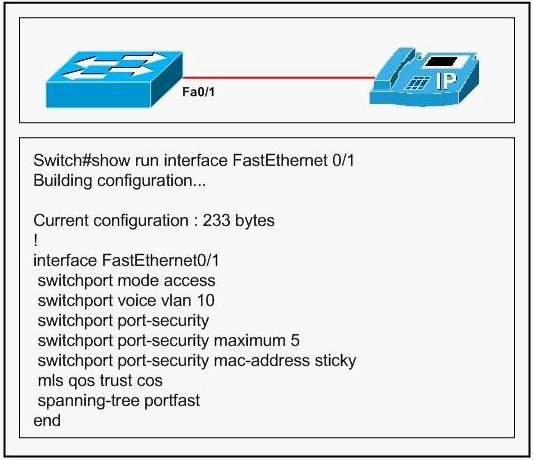
What is the problem with this configuration?
What would happen if another device is connected to the port after the maximum number of devices has been reac
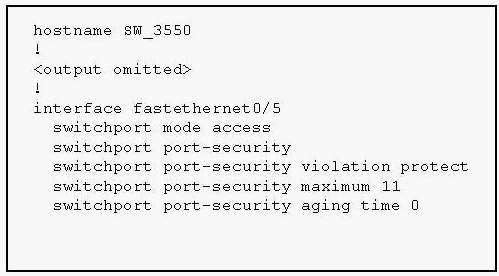
Which statement is true about these threats?
The Company is concerned about Layer 2 security threats. Which statement is true about these threats?
Which procedure would best defend against this type of attack?
An attacker is launching a DoS attack on the Company network using a hacking tool
designed to exhaust the IP address space available from the DHCP servers for a period of
time. Which procedure would best defend against this type of attack?
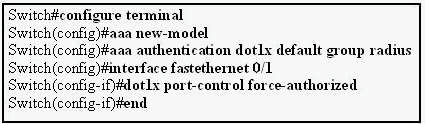
How will interface FastEthernnet0/1 respond when an 802.1x-enabled client connects to the port?
where must 802.1X be configured in order to connect a PC to a switch?
In order to enhance security on the Company network, users must be authenticated using
802.1X. When authentication is required, where must 802.1X be configured in order to
connect a PC to a switch?
Which statement is true about 802.1x port-based authentication?
Company has implemented 802.1X authentication as a security enhancement. Which
statement is true about 802.1x port-based authentication?
Which three statements are true about the dynamic ARP inspection (DAI) feature?
The DAI feature has been implemented in the Company switched LAN. Which three
statements are true about the dynamic ARP inspection (DAI) feature? (Select three)
which three protocols are allowed through the switch port before authentication takes place?
In the use of 802.1X access control, which three protocols are allowed through the switch
port before authentication takes place? Select three.
Which three steps are required?
As the network technician at Company, you need to configure DHCP snooping on a new
switch. Which three steps are required? (Select 3)