Which two statements are true?
A network administrator needs to configure port security on a switch. Which two statements are
true? (Choose two.)
Which two of these changes are necessary for SwitchA to meet the requirements?
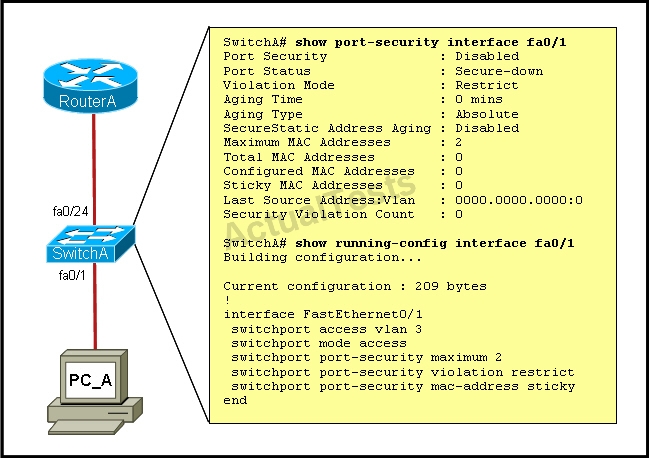
A junior network administrator was given the task of configuring port security on SwitchA to allow
only PC_A to access the switched network through port fa0/1. If any other device is detected, the
port is to drop frames from this device. The administrator configured the interface and tested it with
successful pings from PC_A to RouterA, and then observes the output from these two show
commands.
Which two of these changes are necessary for SwitchA to meet the requirements? (Choose two.)
Which set of commands is recommended to prevent the use of a hub in the access layer?
Which set of commands is recommended to prevent the use of a hub in the access layer?
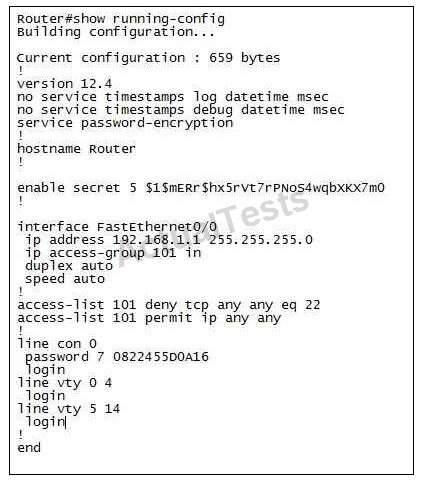
How does using the service password-encryption command on a router provide additional security?
How does using the service password-encryption command on a router provide additional
security?
How can the ACL statements be re-arranged so that the system works as intended?
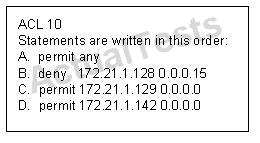
Statements A, B, C, and D of ACL 10 have been entered in the shown order and applied to
interface E0 inbound, to prevent all hosts (except those whose addresses are the first and last IP
of subnet 172.21.1.128/28) from accessing the network. But as is, the ACL does not restrict
anyone from the network. How can the ACL statements be re-arranged so that the system works
as intended?
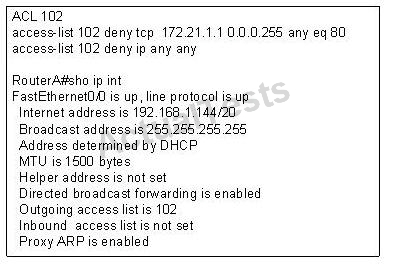
Which interface command immediately removes the effect of ACL 102?
Which Cisco Catalyst feature automatically disables the port in an operational PortFast upon receipt of a BPDU
Which Cisco Catalyst feature automatically disables the port in an operational PortFast upon
receipt of a BPDU?
which interfaces are affected by the ACL?
When you are troubleshooting an ACL issue on a router, which command would you use to verify
which interfaces are affected by the ACL?
The task is to create and apply an access-list with no more than three statements that will allow ONLY host C
CORRECT TEXT
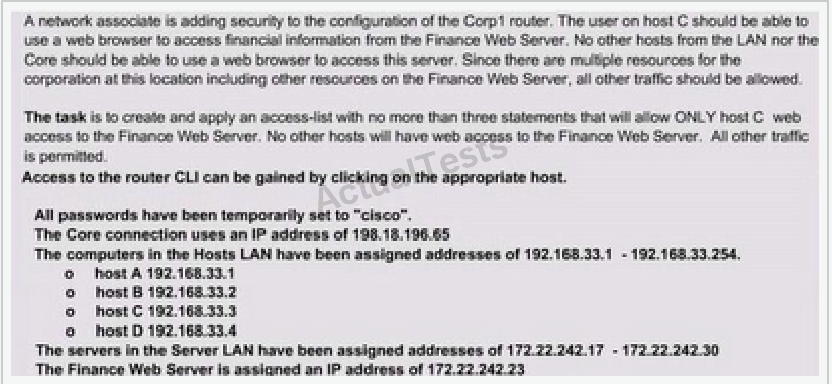
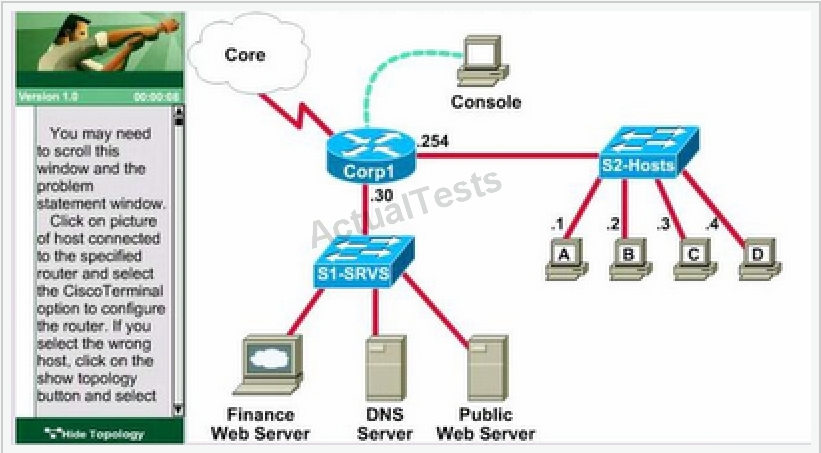
A network associate is adding security to the configuration of the Corp1 router. The user on host C
should be able to use a web browser to access financial information from the Finance Web Server.
No other hosts from the LAN nor the Core should be able to use a web browser to access this
server. Since there are multiple resources for the corporation at this location including other
resources on the Finance Web Server, all other traffic should be allowed.
The task is to create and apply an access-list with no more than three statements that will allow
ONLY host C web access to the Finance Web Server. No other hosts will have web access to the
Finance Web Server. All other traffic is permitted.
Access to the router CLI can be gained by clicking on the appropriate host.
All passwords have been temporarily set to “cisco”.
The Core connection uses an IP address of 198.18.196.65
The computers in the Hosts LAN have been assigned addresses of 192.168.33.1 -192.168.33.254
Host A 192.168.33.1
Host B 192.168.33.2
Host C 192.168.33.3
Host D 192.168.33.4
The servers in the Server LAN have been assigned addresses of 172.22.242.17 – 172.22.242.30
The Finance Web Server is assigned an IP address of 172.22.242.23.