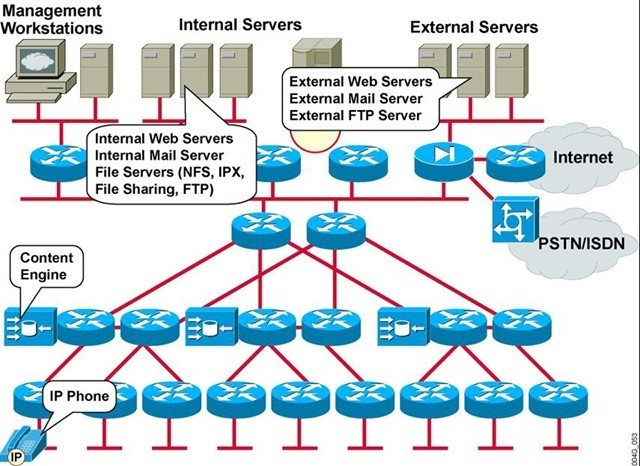
Which element or elements of the existing network infrastructure does this network map emphasize?
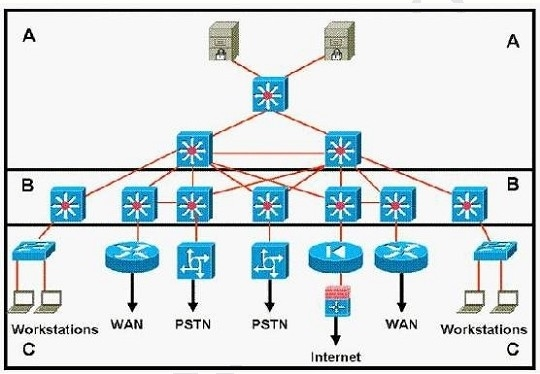
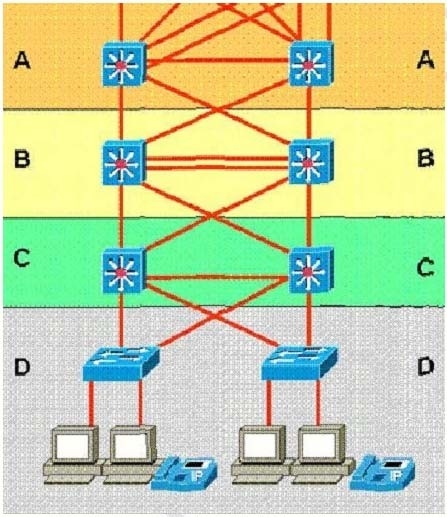
Which statement accurately represents the characteristics of the core layer in this design?
Which Cisco security management solution provides the means to identify, isolate, and counter security.threats
Which Cisco security management solution provides the means to identify, isolate, and counter security
threats to the network?
Which three types of WAN topologies can be deployed in the Cisco Enterprise Architecture Enterprise.Edge WAN m
Which three types of WAN topologies can be deployed in the Cisco Enterprise Architecture Enterprise
Edge WAN module? (Choose three.)
Which two statements correctly identify the layers of the Enterprise Campus module?
How many calls can be made?
Given a VoIP network with these attributes:
Codec: G.728
Bit rate: 16 Kbps
WAN Bandwidth: 256 Kbps
Packet Header: 6 bytes
Payload: 40 bytes
CRTP: Yes
How many calls can be made?
Which three security measures can be used to mitigate DoS attacks that are directed at exposed hosts.within th
Which three security measures can be used to mitigate DoS attacks that are directed at exposed hosts
within the E-Commerce module? (Choose three.)
which network scenario is static routing most appropriate?
For which network scenario is static routing most appropriate?
Which three mechanisms are required to deploy QoS on an IP WAN?
Which three mechanisms are required to deploy QoS on an IP WAN? (Choose three.)
Which H.323 protocol monitors calls for factors such as packet counts, packet loss, and arrival jitter?
Which H.323 protocol monitors calls for factors such as packet counts, packet loss, and arrival jitter?