What describes a technique, used to encapsulate voice (NOT data) over ATM?
What describes a technique, used to encapsulate voice (NOT data) over ATM?
SSL Session ID is used to:
SSL Session ID is used to:
What can be done to affect this without losing any of the updates?
A router is receiving updates for a subnet from different routing protocols. The administrator wishes to take advantage of a path via a route with a less favorable Administrative Distance. What can be done to affect this without losing any of the updates?
When this is detected, the retransmission is sent by:.Exhibit:
You work as a network engineer at domain .com. Study the topology exhibit carefully. Host domain .com 1 and Host domain .com 2 are on Ethernet LANs in different buildings. A serial line is installed between two Cisco routers using Cisco HDLC serial line encapsulation. Routers domain .com A and domain .com B are configured to route IP traffic. Host domain .com 1 sends a packet to Host domain .com 2. A line hit on the serial line causes an error in the packet. When this is detected, the retransmission is sent by:
Exhibit:
The NNI specification defines communications between:
The NNI specification defines communications between:
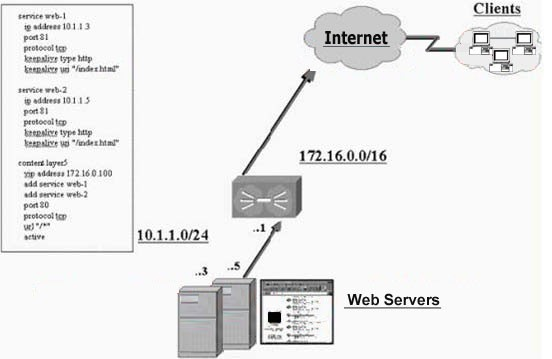
hown diagram the two web servers are configured for port 81 and the content rule for port 80. If a client wish
how is the cipher suite negotiated?
In the SSL handshake, how is the cipher suite negotiated?
A root CA certificate distinguishes itself from other certificates because:
A root CA certificate distinguishes itself from other certificates because:
The configuration register does NOT retain settings for:
The configuration register does NOT retain settings for:
Commercial browsers such as Netscape or Internet Explorer have knowledge of existing root CA certificates beca
Commercial browsers such as Netscape or Internet Explorer have knowledge of existing root CA certificates because: