which of the following traffic is permitted based on the current Access Rules?
What is the best way to mitigate Browser Helper Objects (BHO) from being installed on your system?
What is the best way to mitigate Browser Helper Objects (BHO) from being installed on your system?
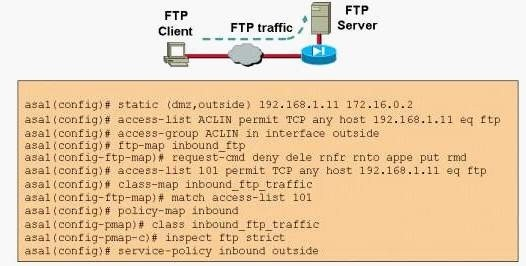
which of the following FTP application answers is correct?
Which is a function of a Cisco router acting as a Network Access Device (NAD ) in a NAC Framework solution ?
Which is a function of a Cisco router acting as a Network Access Device (NAD ) in a NAC Framework solution ?
which of the following entity signs a user’s public key?
With PGP, which of the following entity signs a user’s public key?
What are two key characteristics of VTP?
What are two key characteristics of VTP? (Choose 2)
What is the main reason for using the “ip ips deny-action ips-interface” IOS command?
What is the main reason for using the “ip ips deny-action ips-interface” IOS command?
what should be done at a firewall level to ensure that the protocol is being used correctly?
Since HTTP is one of the most common protocols used in the internet, what should be done at a firewall level to ensure that the protocol is being used correctly?
What aspect of RFC 791 (Internet Protocol) can the attacker exploit to perform this attack?
An attacker is attempting to Telnet to a specific host secured behind a firewall rule that only allows inbound connections on TCP port 25. What aspect of RFC 791 (Internet Protocol) can the attacker exploit to perform this attack?
which context do you allocate interfaces?
When configuring the FWSM for multiple security contexts in which context do you allocate interfaces?