The application can
You are the Cisco Unified Communications Manager in Certpaper.com. After you add the Tcl paramspace command, the application can____.
How can this be accomplished?
When an external call is placed from Ajax, they would like the ANI that is sent to the PSTN to be the main number, not the extension. For domestic calls, they would like 10 digits sent; for international calls, they would like to send the country code 1 and the 10 digits. How can this be accomplished?
The relationship between a Region and a Location
The relationship between a Region and a Location is that the Region codec parameter is used between a Region and its configured Locations.
DRAG DROP
Which Cisco IOS command is used to verify
Which Cisco IOS command is used to verify that a SAF Forwarder that is registered with Cisco Unified Communications Manager has established neighbor relations with an adjacent SAF Forwarder?
how does the calling number get normalized to a global
When an incoming PSTN call arrives at an MGCP gateway, how does the calling number get normalized to a global E.164 number with the + prefix in Cisco Unified Communications Manager?
What is the default value for the Drop Ad Hoc Conference service parameter?
What is the default value for the Drop Ad Hoc Conference service parameter? (Source:Preventing Toll Fraud)
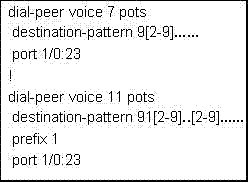
Which statement about the route pattern is true?
The following exhibit shows configs for H.323 gateway. You have been asked to implement TEHO from a remote branch office with area code 301 to the HQ office with area code 201 using Cisco Unified Communications Manager. The remote office has an MGCP gateway and the HQ office has an H.323 gateway. Once the call arrives at the HQ, it should break out to the PSTN as a seven-digit local call. Which statement about the route pattern is true?
Which two statements about symmetric encryption are true?
Which two statements about symmetric encryption are true? (Choose two.) (Source:
Understanding Cryptographic Fundamentals)
which two tasks?
Enabling authentication and encryption for CTI, JTAPI, and TAPI applications requires which two tasks? (Choose two.) (Source: Configuring Cisco IP Telephony Authentication and Encryption)