What is one kind of data these graphs show?
Cisco ASDM provides 16 different graphs that help identify security risks by displaying data about potentially malicious activity. What is one kind of data these graphs show?
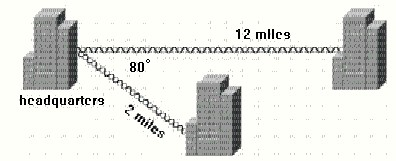
Which antenna is the best to use in this situation?
Which three steps are required to secure this environment?
After properly configuring multiple VLANs, an administrator has decided to secure its VLAN network. Which three steps are required to secure this environment? (Choose three.)
What are two important approaches to communicate when identifying a customer’s security risks?
What are two important approaches to communicate when identifying a customer’s security risks? (Choose two.)
Which tools on Cisco.com could you use to plan for correct Cisco IOS images to support a customer’s secu
Which tools on Cisco.com could you use to plan for correct Cisco IOS images to support a customer’s security design and requirements? (Choose two.)
Which two of these statements best describe fast secure roaming?
Which two of these statements best describe fast secure roaming? (Choose two.)
Which two of these statements describe important aspects of performing a wireless site survey?
Which two of these statements describe important aspects of performing a wireless site survey? (Choose two.)
Which of these is a benefit of an integrated security management system?
Which of these is a benefit of an integrated security management system?
Which item is a feature of Cisco Compatible Extensions, Version 3?
Which item is a feature of Cisco Compatible Extensions, Version 3?
which three of these security benefits?
Cisco ISR Routers offer which three of these security benefits? (Choose three.)