Two packets are considered similar:
Below is the Log and Alert Page of the Global Properties window.
Exhibit missing
The Excessive log grace period field sets the minimum amount of time (in seconds) (The above
not available picture showed 62 seconds) between consecutive logs of similar packets. Two
packets are considered similar:
Which position of a URL is sent to a UFP server when using a TCP resource?
Which position of a URL is sent to a UFP server when using a TCP resource?
For standard RFC (Request for Comments) complaint IKE VPN’s, a user’s authentication method should
For standard RFC (Request for Comments) complaint IKE VPN’s, a user’s authentication method
should be defined where?
When you install the Management Module and GUI Client on a Windows NT Server:
When you install the Management Module and GUI Client on a Windows NT Server:
Receivers then authenticate senders’ public keys, by matching the CA public keys to the CA private keys
The following steps correctly list the actions taken by a Certificate Authority (CA)
1. Users send their public keys to a CA in a secure manner.
2. The CA signs the public keys with its own private keys, creating CA public keys.
3. The CA creates a certificate with its public and private keys.
Receivers then authenticate senders’ public keys, by matching the CA public keys to the CA
private keys on the certificates.
Which of the following will cause VPN-1/Firewall-1 to reset TCP connections with a server protected by SYNDefe
With Secure Client, if you have more than one network adapter: (Choose all that apply)
With Secure Client, if you have more than one network adapter: (Choose all that apply)
Which load-balancing method chooses the physical server closest to the client, based on DNS?
Which load-balancing method chooses the physical server closest to the client, based on DNS?
which the following operating systems does Check Point support installation of the VPN-1/Firewall-1 Management
On which the following operating systems does Check Point support installation of the VPN-1/Firewall-1 Management Server?
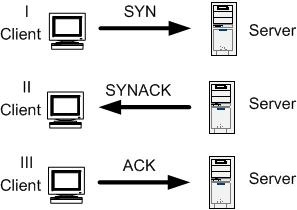
SYN flood attacks are used in the Denial-of-Service (Dos) attacks, or in conjunction with other exploits to bl
SYN flood attacks are used in the Denial-of-Service (Dos) attacks, or in conjunction with other
exploits to block access to a server network.