Which of the following is not an MDS level process?
Which of the following is not an MDS level process?
Which action changes the CMA connection candidates search interval?
The main MDS process (fwm mds) looks for CMAs which are up and can be reached, but with
which it has no CPMI connections. This connection is used for collecting statuses on the CMA and
its gateways, and for receiving changes in objects that are relevant to the MDS/MDG system.
Normally, a special task wakes up every 120 seconds and searches for “CMA connection
candidates”. If the task has found connection candidates previously, then by default it wakes up
after only 90 seconds. This shorter interval boosts CMAs connections upon MDS startup. Which
action changes the CMA connection candidates search interval?
Which action changes the status collection interval?
The main MDS process (fwm mds) looks for CMAs which are up and can be reached, but with
which it has no CPMI connections. This connection is used for collecting statuses on the CMA and
its gateways, and for receiving changes in objects that are relevant to the MDS/MDG system.
Normally, a special task wakes up every 120 seconds and searches for “CMA connection
candidates”. If the task has found connection candidates previously, then by default it wakes up
after only 90 seconds. This shorter interval boosts CMAs connections upon MDS startup. Which
action changes the status collection interval?
which the P1 shell saves all its logs?
Where is the text file located in which the P1 shell saves all its logs?
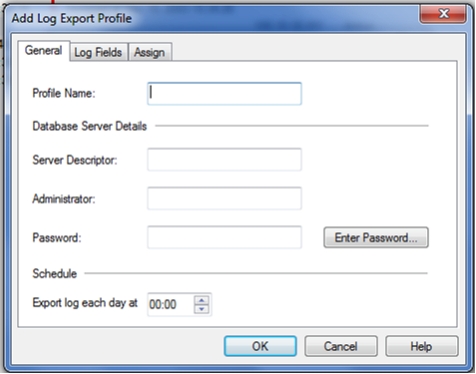
What is correct about the screen below?
How do you establish a secure connection to generate reports in SmartReporter using data from this log server?
One Firewall in a Multi-Domain Management with Provider-1 environment delivers log data to a
local log server, placed in the same LAN as the Firewall. This log server is connected to and
managed by the CMA that manages the Firewall.
How do you establish a secure connection to generate reports in SmartReporter using data from
this log server?
True or False: You can install Global security rules on Security Gateways, Edge gateways, SmartProvisioning pr
True or False: You can install Global security rules on Security Gateways, Edge gateways,
SmartProvisioning profiles, and Open Security Extensions (OSE) devices.
Is he right or is there a better way?
Tom has been asked to add a rule that applies to only the perimeter firewalls and not the internal
firewalls of all the customers managed by Multi-Domain Management with Provider-1. He sees
that there is one single global policy assigned to all the customers and feels very happy that he will
have to just add one rule in that global policy and reassign and install the policy to all the
customers at once. While doing so, he realizes that this action will also install the rule on the
internal firewalls managed by the CMA’s. He’s afraid that he will now have to put the rule in each
individual policy applied to perimeter gateways. Is he right or is there a better way?
what happens if this host is deleted within the Global SmartDashboard?
In the Global Rule Base, global objects are used. Suppose that one of these objects is a Host
Node that you would like to remove. However, an older Global Rule Base is using this object, and
this policy is currently assigned to a customer. 
what happens if this host is deleted within the Global SmartDashboard?
How do you configure this requirement?
When configuring a Global Rule Base, you discover that it is necessary to define a NAT rule. How
do you configure this requirement?