Which of the following configurations is MOST appropriate for Jerry?
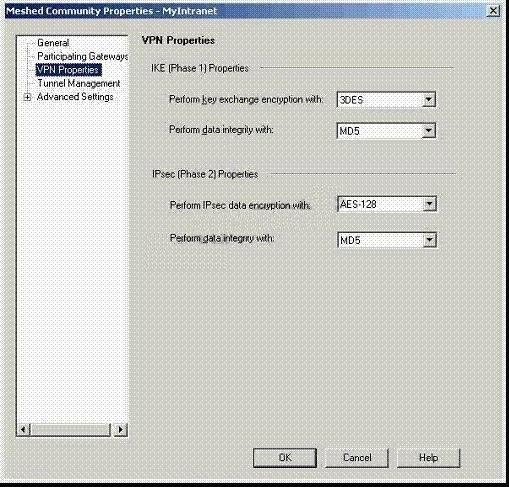
Jerry is concerned that a denial-oF. service (DoS) attack may affect his VPN Communities. He
decides to implement IKE DoS protection. Jerry needs to minimize the performance impact of
implementing this new protection. Which of the following configurations is MOST appropriate for
Jerry?
Where can a Security Administrator adjust the unit of measurement (bps, Kbps or Bps), for Check Point QoS band
Where can a Security Administrator adjust the unit of measurement (bps, Kbps or Bps), for Check
Point QoS bandwidth?
What is the best Load Sharing method for preventing this type of problem?
Problems sometimes occur when distributing IPSec packets to a few machines in a Load Sharing
Multicast mode cluster, even though the machines have the same source and destination IP
addresses. What is the best Load Sharing method for preventing this type of problem?
What is the best Load Sharing method for preventing this type of problem?
Problems sometimes occur when distributing IPSec packets to a few machines in a Load Sharing
Multicast mode cluster, even though the machines have the same source and destination IP
addresses. What is the best Load Sharing method for preventing this type of problem?
Which of the following statements is TRUE?
which FTP commands pass through the Security Gateway protecting the FTP servers?
Rachel is the Security Administrator for a university. The university’s FTP servers have old
hardware and software. Certain FTP commands cause the FTP servers to malfunction. Upgrading
the FTP servers is not an option at this time. Which of the following options will allow Rachel to
control which FTP commands pass through the Security Gateway protecting the FTP servers?
which FTP commands pass through the Security Gateway protecting the FTP servers?
Rachel is the Security Administrator for a university. The university’s FTP servers have old
hardware and software. Certain FTP commands cause the FTP servers to malfunction. Upgrading
the FTP servers is not an option at this time. Which of the following options will allow Rachel to
control which FTP commands pass through the Security Gateway protecting the FTP servers?
What causes the Connection Rejection?
You are reviewing SmartView Tracker entries, and see a Connection Rejection on a Check Point
QoS rule. What causes the Connection Rejection?
What could cause this behavior?
Wayne configures an HTTP Security Server to work with the content vectoring protocol to screen
forbidden sites. He has created a URI resource object using CVP with the following settings:
Use CVP
Allow CVP server to modify content
Return data after content is approved
He adds two rules to his Rule Base: one to inspect HTTP traffic going to known forbidden sites,
the other to allow all other HTTP traffic.
Wayne sees HTTP traffic going to those problematic sites is not prohibited.
What could cause this behavior?
What is the problem, and how do you fix it?
You want to block corporate internal-net and localnet from accessing Web sites containing
inappropriate content. You are using WebTrends for URL filtering. You have disabled VPN-1
Control connections in the Global properties. Review the diagram and the Security Policies for
GW_A and GW_B in the exhibit provided.
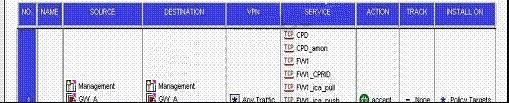
Corporate users and localnet users receive message “Web cannot be displayed”. In SmartView
Tracker, you see the connections are dropped with message “content security is not reachable”.
What is the problem, and how do you fix it?