Which of the following modes allows a client in a load-balancing environment to retain its connection with the
Which of the following modes allows a client in a load-balancing environment to retain its
connection with the same server during a session?
Which of the following VPN-1/FireWall-1 installation options is MOST appropriate for Dr King’s environme
Dr Billis a Security Administrator preparing to install and deploy VPN-1/FireWall-1 to protect his
company’s information assets. Dr Billonly has one machine to dedicate to security enforcement.
Which of the following VPN-1/FireWall-1 installation options is MOST appropriate for Dr King’s
environment?
Why is the user NOT listed?
Dr Billis a VPN-1/FireWall-1 Security Administrator attempting to implement SecuRemote access.
Dr Billcreates and configures a SecuRemote user. When he goes to his RemoteAccess
Community and attempts to add the new user as a participant, the user is not listed. Why is the
user NOT listed?
What is the proper order to uninstall VPN-1/FirwWall-1 in a stand-alone configuration?
What is the proper order to uninstall VPN-1/FirwWall-1 in a stand-alone configuration?
SmartConsolesSVN FoundationVPN-1/FireWall-1Policy Server
A digital signature:
A digital signature:
Which of the following is the BEST explanation for the failure?
Dr Billis a Security Administrator who must define a new user for SecuRemote access to his VPN-1/FireWall-1 VPN Domain. Dr Billhas an established Remote Access VPN community for existing
SecuRemote users. Dr Billcreates a new user and populates the Login Name field. He then saves
and installs the Security Policy. When Dr Billattempts a SecuRemote connection using the newly
created user, the connection fails. Which of the following is the BEST explanation for the failure?
Which of the following should Dr Billconfigure?
Dr Billwants to configure a custom script to launch an application for certain rules. Which of the
following should Dr Billconfigure?
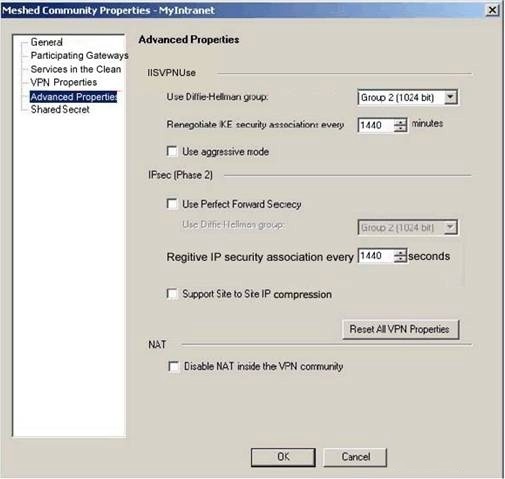
Which of the following will end the intruder’s access after the next Phase 2 exchange occurs?
Assume an intruder has succeeded in compromising your current IKE Phase 1 and Phase 2 keys.
Which of the following will end the intruder’s access after the next Phase 2 exchange occurs?
which of the following?
To enable session tracking, you must do which of the following? (Choose two)