In order to achieve these objectives, you:
Your IT boss gives you the following requirements which are classified as mandatory requirements and optional requirements.
Mandatory requirements
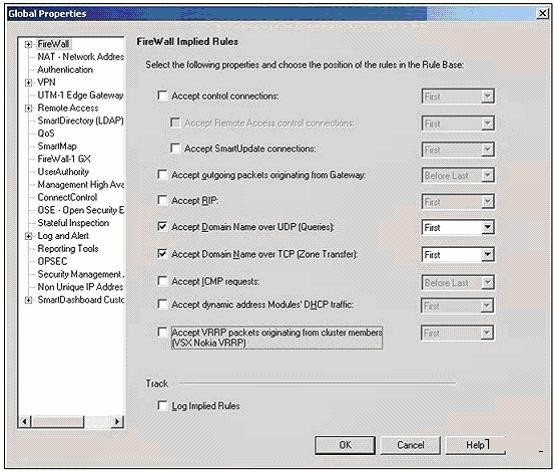
1: Accept domain-name-over-TCP traffic (zone-transfer traffic)
2: Log domain-name-over-TCP traffic (zone- transfer traffic)
Optional requirements
1: Accept domain-name-over-UDP traffic (queries traffic) Optional requirements
2: Do not log domain-name-over-UDP traffic (queries traffic)
3: Do not clutter the Rule Base by creating explicit rules for traffic that can be controlled using Global Properties. In order to achieve these objectives, you:
Which of the following is true regarding UTM-1 Edge appliances?
Which of the following is true regarding UTM-1 Edge appliances?
Why must Client Authentication rule be placed above Stealth rule in the Rulebase?
Why must Client Authentication rule be placed above Stealth rule in the Rulebase?
External User Profiles can be defined as:
External User Profiles can be defined as:
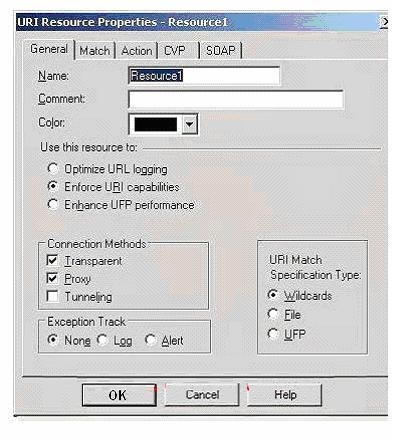
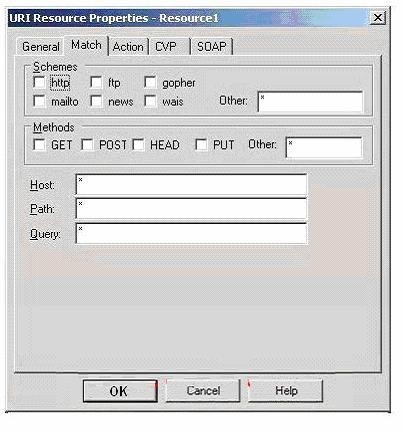
From the answer options below, select all the URI Match Specification type you can choose from in the General
What rule is shown in the diagram?
When running this command with the -boot option, then the:
The cprinstall install command is used to install Check Point products on remote modules. When running this command with the -boot option, then the:
The log file for the Eventia Reporter server can be found in the in which location?
The log file for the Eventia Reporter server can be found in the in which location?
At what point does policy get downloaded from a policy server?
At what point does policy get downloaded from a policy server?
Once you have successfully upgraded Security Management server, what tool will you use to manage your contract
Once you have successfully upgraded Security Management server, what tool will you use to manage your contracts?