which type of network traffic?
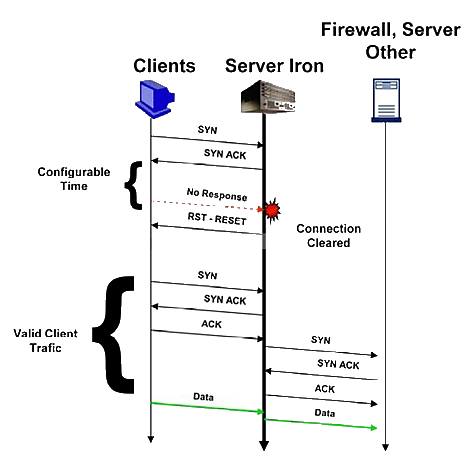
Syn-proxy applies to which type of network traffic?
Which embedded security feature can be used to match the payload and drop the offending packet?
The exhibit shows the payload of a worm that attacks Web servers.
Which embedded security feature can be used to match the payload and drop the offending
packet?
What will happen when applying this command on the Brocade ADX?
Given the command shown below:
ServerIron# server prioritize-mgmt-traffic 1.1.1.0 255.255.255.0 200.1.1.1 6 22
What will happen when applying this command on the Brocade ADX?
What are two results after performing this configuration?
A Web server is directly attached to interface 1 of the Brocade ADX.
What are two results after performing this configuration? (Choose two.)
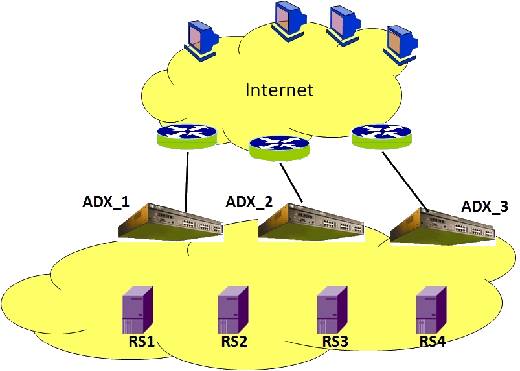
which two statements are true?
Which command is safe to remove from the configuration?
You are performing routine housekeeping on your Brocade ADX by reviewing your current
configuration. You have no Layer 7 Health Checks configured on your Brocade ADX.
Which command is safe to remove from the configuration?
what would happen if the gigRegister.html page is missing?
Referring to the exhibit, what would happen if the gigRegister.html page is missing?
What are two options for real server selection?
A Brocade ADX is configured with a transparent VIP using a stateless port for DNS.
What are two options for real server selection? (Choose two.)
how will the Brocade ADX handle requests for port DNS?
Given the configuration shown in the exhibit, how will the Brocade ADX handle requests for port
DNS?