What is one reason for this?
OpenVMS systems are highly resistant to buffer overflow attacks. What is one reason for this?
Why does an OpenVMS system with both internal and external users need to be protected by a hardware firewall?
Why does an OpenVMS system with both internal and external users need to be protected by a
hardware firewall?
Which file will cause auditing messages to be sent to the security operator consoles?
User PHILBY, UIC [SIS,PHILBY], holds rights identifiers LONDON and CAMBRIDGE and
executes the command TYPE *.* in a directory containing the following files. Which file will cause
auditing messages to be sent to the security operator consoles?
which image another process is executing?
How can a system manager identify which image another process is executing?
Which two login modes are subject to intrusion detection?
Which two login modes are subject to intrusion detection? Select two.
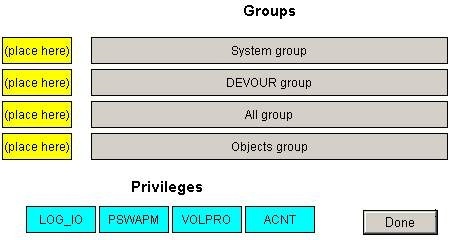
Using drag and drop, match the privileges into the correct privilege groups
Which statement is true regarding the accessible objects?
A system manager running both DECnet and TCP/IP should secure the installation default
network accessible objects (TCP/IP service or DECnet session control application). Which
statement is true regarding the accessible objects?
Which privilege and/or access right is needed to MOUNT/FOREIGN a FILES-11 volume?
Which privilege and/or access right is needed to MOUNT/FOREIGN a FILES-11 volume?
in AUTHORIZE)?
Which two options are valid access modes (e.g. in AUTHORIZE)? Select two.
what is the security context of an executing application based?
On what is the security context of an executing application based?