What are the benefits of implementing bladed architectu…
What are the benefits of implementing bladed architecture instead of traditional rack mount servers? (Select two.)
Which HPE BladeSystem component is needed to be able to…
A customer is deploying a new solution that requires a third-party VoIP card.
Which HPE BladeSystem component is needed to be able to attach the customer’s existing BL460c Gen9
server blades to the VoIP card?
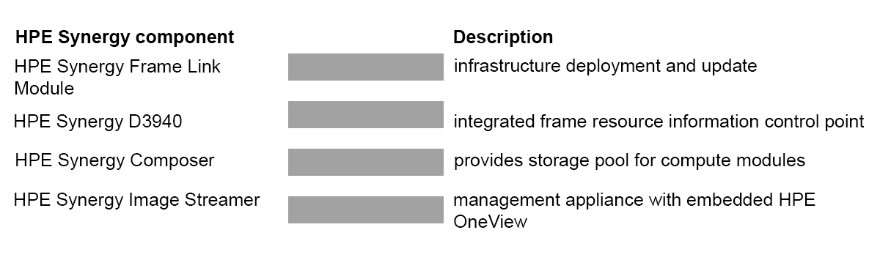
Click and drag each HPE Synergy component on the left to match…
Which solution should the architect recommend to the cu…
A customer needs to eliminate thermal imbalance in its new data center.
Which solution should the architect recommend to the customer?
How many FlexNICs will be available per 20Gb port for t…
A customer selects the HPE c7000 with redundant FlexFabric-20/40 F8 Virtual Connect modules for a private
cloud project. For the server platform, the customer plans to use the ProLiant BL460 Gen9 with the FlexFabric
adapters installed.
How many FlexNICs will be available per 20Gb port for the customer’s cloud services?
What is a feature of HPE Onboard Administrator?
What is a feature of HPE Onboard Administrator?
Which solution should the architect recommend to achiev…
A customer’s database is slow to respond, and the customer meets response times to be dramatically
increased.
Which solution should the architect recommend to achieve this result?
What should the administrator do to separate traffic?
A system administrator is concerned about a high number of visitors connecting to a company’s network. In
addition to the production network traffic, the network infrastructure is used for the systems management traffic
to the company’s servers.
What should the administrator do to separate traffic?
Which array controller should the architect recommend f…
A customer is considering the DL380 Gen9 as the platform standard for its VLAN cluster. The configuration will
use 24 drives. Each 8-drive cage will contain 1 SSD and 7 SATA drives.
Which array controller should the architect recommend for this configuration?
Which methods can an administrator implement to provide…
Which methods can an administrator implement to provide higher security within a management network?
(Select two.)